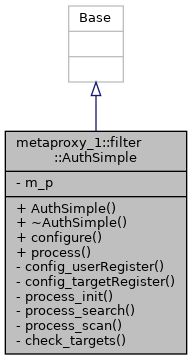
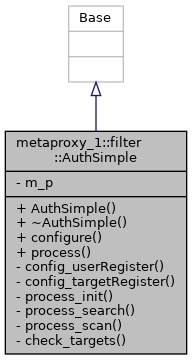
#include <filter_auth_simple.hpp>
Definition at line 28 of file filter_auth_simple.hpp.
◆ AuthSimple()
| mp::filter::AuthSimple::AuthSimple |
( |
| ) |
|
◆ ~AuthSimple()
| mp::filter::AuthSimple::~AuthSimple |
( |
| ) |
|
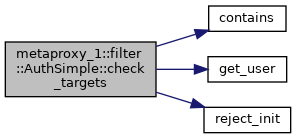
◆ check_targets()
| void mp::filter::AuthSimple::check_targets |
( |
metaproxy_1::Package & |
package | ) |
const |
|
private |
Definition at line 388 of file filter_auth_simple.cpp.
390 Z_InitRequest *initReq = package.request().get()->u.z3950->u.initRequest;
392 std::string password;
393 std::string user =
get_user(initReq, password);
394 std::list<std::string> authorisedTargets =
m_p->targetsByUser[user];
396 std::list<std::string> targets;
397 Z_OtherInformation **otherInfo = &initReq->otherInfo;
398 mp::util::remove_vhost_otherinfo(otherInfo, targets);
401 std::list<std::string>::iterator i;
404 while (i != targets.end()) {
405 if (
contains(authorisedTargets, *i) ||
409 if (!
m_p->discardUnauthorisedTargets)
411 YAZ_BIB1_ACCESS_TO_SPECIFIED_DATABASE_DENIED, i->c_str());
412 i = targets.erase(i);
416 if (targets.size() == 0)
418 YAZ_BIB1_ACCESS_TO_SPECIFIED_DATABASE_DENIED,
422 mp::util::set_vhost_otherinfo(otherInfo, odr, targets);
static bool contains(std::list< std::string > list, std::string thing)
static std::string get_user(Z_InitRequest *initReq, std::string &password)
static void reject_init(mp::Package &package, int err, const char *addinfo)
References contains(), get_user(), and reject_init().
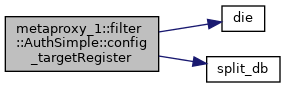
◆ config_targetRegister()
| void mp::filter::AuthSimple::config_targetRegister |
( |
std::string |
filename, |
|
|
const char * |
path |
|
) |
| |
|
private |
Definition at line 197 of file filter_auth_simple.cpp.
201 if (!yaz_filepath_resolve(filename.c_str(), path, 0, fullpath))
202 die(
"Could not open " + filename);
203 std::ifstream fp(fullpath);
205 die(
"Could not open " + filename);
209 fp.getline(buf,
sizeof buf);
210 if (*buf ==
'\0' || *buf ==
'#')
212 char *targetsp = strchr(buf,
':');
214 die(
"auth_simple target-register '" + filename +
"': " +
215 "no targets on line: '" + buf +
"'");
217 std::list<std::string> tmp;
219 m_p->targetsByUser[buf] = tmp;
222 printf(
"Added user '%s' with targets:\n", buf);
223 std::list<std::string>::const_iterator i;
224 for (i = tmp.begin(); i != tmp.end(); i++) {
225 printf(
"\t%s\n", (*i).c_str());
static void split_db(std::list< std::string > &dbs, const char *databasesp)
static void die(std::string s)
References die(), and split_db().
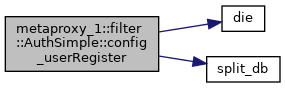
◆ config_userRegister()
| void mp::filter::AuthSimple::config_userRegister |
( |
std::string |
filename, |
|
|
const char * |
path |
|
) |
| |
|
private |
Definition at line 152 of file filter_auth_simple.cpp.
156 if (!yaz_filepath_resolve(filename.c_str(), path, 0, fullpath))
157 die(
"Could not open " + filename);
159 std::ifstream fp(fullpath);
161 die(
"Could not open " + filename);
166 fp.getline(buf,
sizeof buf);
167 if (*buf ==
'\0' || *buf ==
'#')
169 char *passwdp = strchr(buf,
':');
171 die(
"auth_simple user-register '" + filename +
"': " +
172 "no password on line: '" + buf +
"'");
174 char *databasesp = strchr(passwdp,
':');
176 die(
"auth_simple user-register '" + filename +
"': " +
177 "no databases on line: '" + buf +
":" + passwdp +
"'");
179 yf::AuthSimple::Rep::PasswordAndDBs tmp(passwdp);
181 m_p->userRegister[buf] = tmp;
185 printf(
"Added user '%s' -> password '%s'\n", buf, passwdp);
186 std::list<std::string>::const_iterator i;
187 for (i = tmp.dbs.begin(); i != tmp.dbs.end(); i++)
188 printf(
"db '%s'\n", (*i).c_str());
References die(), and split_db().
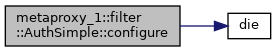
◆ configure()
| void mp::filter::AuthSimple::configure |
( |
const xmlNode * |
ptr, |
|
|
bool |
test_only, |
|
|
const char * |
path |
|
) |
| |
Definition at line 106 of file filter_auth_simple.cpp.
109 std::string userRegisterName;
110 std::string targetRegisterName;
112 for (ptr = ptr->children; ptr != 0; ptr = ptr->next) {
113 if (ptr->type != XML_ELEMENT_NODE)
115 if (!strcmp((
const char *) ptr->name,
"userRegister")) {
116 userRegisterName = mp::xml::get_text(ptr);
117 m_p->got_userRegister =
true;
118 }
else if (!strcmp((
const char *) ptr->name,
"targetRegister")) {
119 targetRegisterName = mp::xml::get_text(ptr);
120 m_p->got_targetRegister =
true;
121 }
else if (!strcmp((
const char *) ptr->name,
122 "discardUnauthorisedTargets")) {
123 m_p->discardUnauthorisedTargets =
true;
125 die(
"Bad element in auth_simple: <"
126 + std::string((
const char *) ptr->name) +
">");
130 if (!
m_p->got_userRegister && !
m_p->got_targetRegister)
131 die(
"auth_simple: no user-register or target-register "
132 "filename specified");
134 if (
m_p->got_userRegister)
136 if (
m_p->got_targetRegister)
References die().
◆ process()
| void mp::filter::AuthSimple::process |
( |
metaproxy_1::Package & |
package | ) |
const |
Definition at line 232 of file filter_auth_simple.cpp.
234 Z_GDU *gdu = package.request().get();
236 if (!gdu || gdu->which != Z_GDU_Z3950) {
240 return package.move();
243 if (
m_p->got_userRegister) {
244 switch (gdu->u.z3950->which) {
261 if (
m_p->got_targetRegister && gdu->u.z3950->which == Z_APDU_initRequest)
265 return package.move();
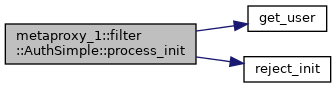
◆ process_init()
| void mp::filter::AuthSimple::process_init |
( |
metaproxy_1::Package & |
package | ) |
const |
|
private |
Definition at line 272 of file filter_auth_simple.cpp.
274 Z_InitRequest *initReq = package.request().get()->u.z3950->u.initRequest;
276 std::string password;
277 std::string user =
get_user(initReq, password);
279 if (user.length() == 0)
280 return reject_init(package, 0,
"no credentials supplied");
282 if (
m_p->userRegister.count(user)) {
284 yf::AuthSimple::Rep::PasswordAndDBs pdbs =
285 m_p->userRegister[user];
286 if (pdbs.password == password) {
289 boost::mutex::scoped_lock lock(
m_p->mutex);
290 m_p->userBySession[package.session()] = user;
292 return package.move();
296 return reject_init(package, 0,
"username/password combination rejected");
References get_user(), and reject_init().
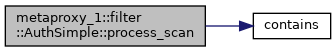
◆ process_scan()
| void mp::filter::AuthSimple::process_scan |
( |
metaproxy_1::Package & |
package | ) |
const |
|
private |
Definition at line 344 of file filter_auth_simple.cpp.
347 package.request().get()->u.z3950->u.scanRequest;
349 if (
m_p->userBySession.count(package.session()) == 0) {
351 return package.move();
354 std::string user =
m_p->userBySession[package.session()];
355 yf::AuthSimple::Rep::PasswordAndDBs pdb =
m_p->userRegister[user];
356 for (
int i = 0; i < req->num_databaseNames; i++) {
357 if (!
contains(pdb.dbs, req->databaseNames[i]) &&
361 Z_APDU *apdu = odr.create_scanResponse(
362 package.request().get()->u.z3950,
363 YAZ_BIB1_ACCESS_TO_SPECIFIED_DATABASE_DENIED,
364 req->databaseNames[i]);
365 package.response() = apdu;
366 package.session().close();
372 return package.move();
References contains().
◆ process_search()
| void mp::filter::AuthSimple::process_search |
( |
metaproxy_1::Package & |
package | ) |
const |
|
private |
Definition at line 312 of file filter_auth_simple.cpp.
314 Z_SearchRequest *req =
315 package.request().get()->u.z3950->u.searchRequest;
317 if (
m_p->userBySession.count(package.session()) == 0) {
319 return package.move();
322 std::string user =
m_p->userBySession[package.session()];
323 yf::AuthSimple::Rep::PasswordAndDBs pdb =
m_p->userRegister[user];
324 for (
int i = 0; i < req->num_databaseNames; i++) {
325 if (!
contains(pdb.dbs, req->databaseNames[i]) &&
329 Z_APDU *apdu = odr.create_searchResponse(
330 package.request().get()->u.z3950,
331 YAZ_BIB1_ACCESS_TO_SPECIFIED_DATABASE_DENIED,
332 req->databaseNames[i]);
333 package.response() = apdu;
334 package.session().close();
340 return package.move();
References contains().
◆ m_p
| boost::scoped_ptr<Rep> metaproxy_1::filter::AuthSimple::m_p |
|
private |
The documentation for this class was generated from the following files: